HARDENED SYSTEM
HARDENED SYSTEM
AOSP's build process has been strengthened, including improvements for stack probes, bounds checking, frame pointers and automatic variable initialization. The compiler toolchain and libc have been hardened. hardened_malloc has been tuned to increase entropy, quarantine space and overall security at the expense of performance.
 HARDENED SETTINGS
HARDENED SETTINGS
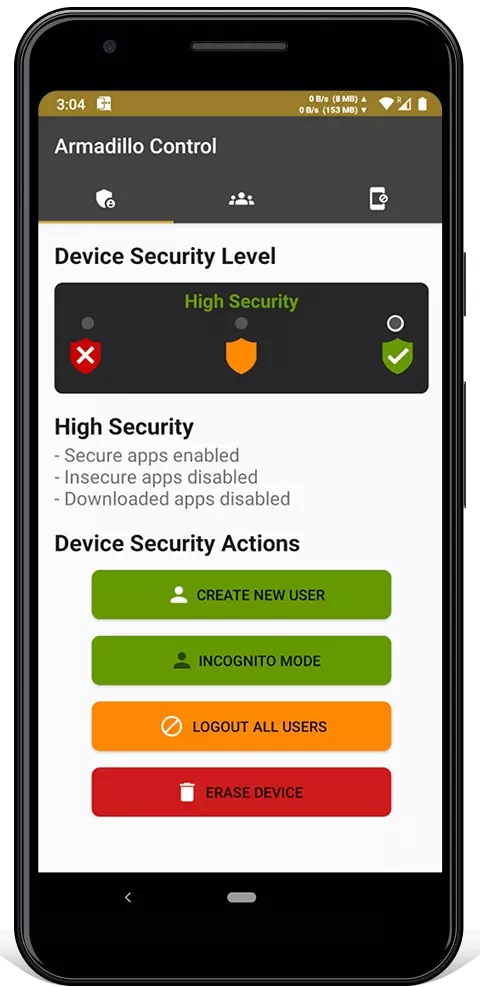
Safe default settings have been set, such as requiring strong passwords, hiding notification content and disabling biometrics. If your Armadillo Phone is remotely wiped, it won't indicate it's erasing your data. The ability to toggle Wi-Fi, Bluetooth or airplane mode from a locked phone has been disabled.
 HARDENED MEDIA
HARDENED MEDIA
Historically, the Android media stack has been very vulnerable, so Armadillo has hardened it to resist attacks. The oldest, least used and riskiest codecs ( such as H263 and software codecs ) have been removed. Scudo has been expanded in scope and hardened. The mediadrmserver and drmserver have been removed.
 HARDENED
HARDENED
NETWORKING
All Armadillo apps uses TLS multiplexing with pinned TLS certificates. TLS multiplexing prevents leaking protocol metadata and bypasses firewalls. Network time is synchronized using TLS, instead of NTP. Name resolution is done using DoT ( DNS over TLS ) instead of plaintext DNS. TLS session tickets are disabled to prevent tracking across connections.
 HARDENED
HARDENED
APPS
MMS auto-retrieval is permanently disabled in the SMS app to mitigate remote attacks.
Dangerous permissions (like internet or location access) given to the Camera and Contacts apps have been removed.
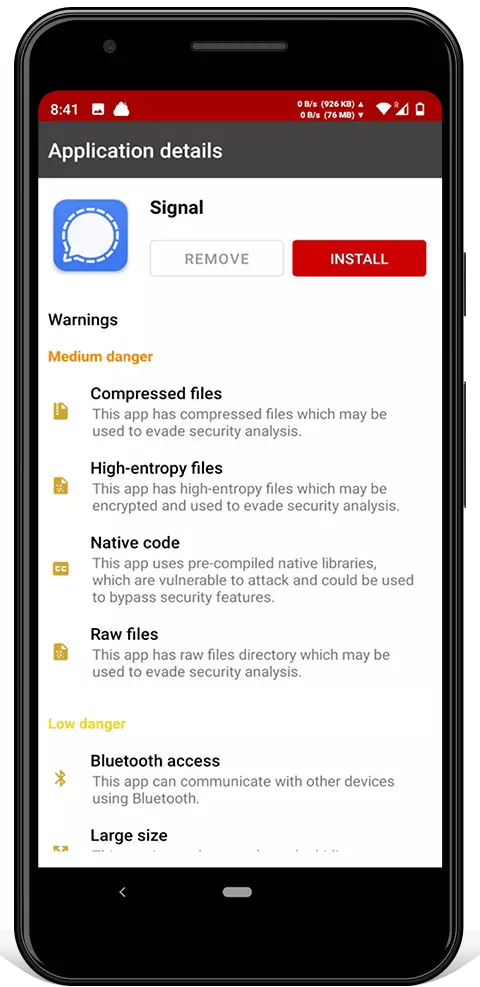
All apps are clearly coloured and labeled as either "insecure" or "secure" to prevent user confusion.
 REDUCED
REDUCED
ATTACK SURFACE
Unsafe software components have been removed to prevent vulnerabilities. This includes tracking software used by Google and third-parties. .
There is no web browser app installed by default.

 ARMADILLO BEACON
ARMADILLO BEACON Armadillo Protect: Detect and prevent mobile attacks from compromising your Armadillo Phone.
Armadillo Protect: Detect and prevent mobile attacks from compromising your Armadillo Phone.